How to Protect Your Business by Limiting Attack Dwell Time
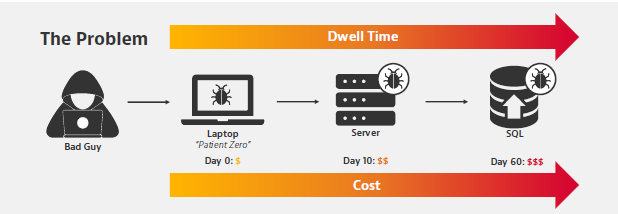
Security breaches and cyberattacks are a constant threat. Network and security teams must take proactive steps to protect their systems from these attacks, but it is difficult to stay ahead of the malicious actors. Instead of solely relying on prevention, it is important to have plans in place to quickly identify a breach, and minimize the amount of time the malicious actors have access to the system, known as dwell time. Having an effective plan in place to identify a breach and reduce the dwell time is essential to protecting the system from the malicious actors. By having an effective plan in place, the malicious actors have less time to cause damage and access sensitive information. Additionally, quickly identifying and disabling a breach can help limit the amount of damage caused and reduce the likelihood of a successful attack.
In this whitepaper “How to Protect Your Business by Limiting Attack Dwell Time”, you will discover a strategy to reduce the impact of a breach and strengthen existing security initiatives with integrated threat analysis.
Malicious actors may be a step ahead but being proactive and prepared can help to limit the damage they can cause. By having a plan in place to anticipate and respond to malicious activities, companies can protect their systems, finances, reputation, and customers. This could include regularly applying security patches, using multi-factor authentication, and monitoring for suspicious activity. Additionally, companies should have a plan for responding quickly and effectively to any security incidents. This could include having a team dedicated to responding to cyber threats, as well as developing a communication plan to keep stakeholders informed. By being proactive and prepared, companies can reduce the impact of malicious activity on their business.
We hope you find this information helpful. If you have any questions or would like to see the VIAVI Observer in action, please contact us here or speak to one of our friendly team members on 0393817888
The VIAVI Observer Platform in a Nutshell
The VIAVI Observer platform is a comprehensive system designed to help identify suspicious events in a network. It provides deep insights into the data flowing through the network, allowing businesses to detect and investigate any malicious activity. The system uses machine learning algorithms to analyze the data, and can quickly determine the severity of the event. It can also be used to white-list trusted hosts and devices, helping businesses to identify the source of any breaches. Additionally, the system can be used to monitor IP blacklists, providing an extra layer of security against malicious traffic. The VIAVI Observer platform is easy to use and can be deployed in a single box, making it an ideal solution for businesses looking for an effective way to protect their business against security breaches and cyberattacks.