The truth is, the danger of cyber attacks has reached alarming heights, and it's a secret that can no longer be ignored. Businesses in all kinds of industries are dealing with more advanced and sophisticated threats that can compromise their networks, systems, and valuable data. In this situation, it's incredibly important to understand the significance of network monitoring and DDoS (Distributed Denial of Service) resilience testing. These practices are essential in reducing risks, protecting the smooth operation of businesses, and ensuring that sensitive information stays secure.
The Changing Cyber Threat Landscape
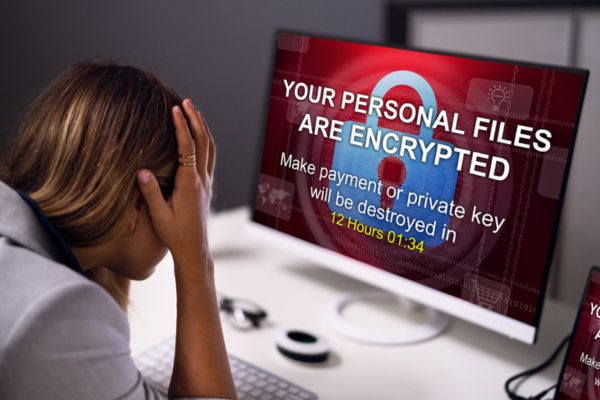
Picture a treacherous cyber battleground, teeming with wicked schemes and deceitful plots. In this digital warzone, a multitude of malicious activities thrive, threatening the very essence of our interconnected world. From sinister ransomware attacks that hold valuable data hostage to cunning Business Email Compromise (BEC) schemes that trick unsuspecting victims, cybercriminals are constantly honing their tactics to exploit any vulnerability they can find. But beware, for there is a looming menace that towers above them all: the dreaded DDoS attacks. These relentless assaults possess the power to cripple networks, wreak havoc on essential services, and unleash devastating blows upon businesses finances and reputation. The battle against cyber threats has never been more critical or urgent.
The Impact on Australian Businesses
Australian businesses are not immune to the impact of cyber attacks, with threat actors targeting critical infrastructure and disrupting operations leading to larger ransom payments. Sadly, with almost a third of businesses willing to pay more than $1 million in ransom payments, research shows that business leaders are starting to treat the ransomware threat as they would any other business risk. The risks and consequences of these attacks can be severe, resulting in significant financial losses and reputational damage. Moreover, businesses may also face legal actions and regulatory compliance issues if they fail to protect sensitive data adequately. It is crucial for businesses to take proactive measures to mitigate these risks and enhance their security posture.
Factors Increasing Vulnerability
Several factors contribute to the increasing vulnerability of businesses to cyber attacks. Sensitive data and financial information have become lucrative targets for attackers, making it imperative for businesses to implement robust security measures. Legacy IT systems, coupled with challenges in educating staff and high turnover rates, create additional vulnerabilities. Moreover, reduced IT spending and weaker security measures further expose businesses to potential threats. Attackers are also known to leverage core mission operations for malicious intent. In this dynamic environment, businesses must stay vigilant and proactive in their approach to cybersecurity.
Valuable Data
Increased likelihood that you hold sensitive information and possibly financial data of significant importance. Information of this nature is a lucrative target for cybercriminals.
Less IT Spend
Free software or inexpensive web hosting / licensing can have weaker security measures, making businesses an easy target for cybercriminals.
Legacy IT
Older computers, or ones that haven’t been diligently updated, are easily vulnerable to attack by cybercriminals and regularly leveraged.
Leverage core mission
Under the pretence of BAU operations, cybercriminals can forward malicious emails to staff that seek to introduce viruses or malware into computer systems.
The Importance of Network Monitoring and DDoS Resilience Testing
Network monitoring and DDoS resilience testing are vital components of a comprehensive cybersecurity strategy. These practices enable businesses to detect and mitigate cyber threats in real-time, allowing them to respond promptly and effectively. By continuously monitoring network traffic and identifying anomalies, businesses can stay ahead of potential breaches and proactively address vulnerabilities. Network monitoring is not only crucial for safeguarding sensitive data but also for ensuring compliance with the ever-increasing number of data privacy regulations.
Network monitoring assumes a pivotal role in a comprehensive cybersecurity framework. By continuously monitoring network traffic and detecting anomalies, businesses gain the ability to proactively identify potential breaches and vulnerabilities. A notable solution in this regard is VIAVI Solutions' Observer Platform, a robust network performance monitoring and diagnostics (NPMD) solution that offers comprehensive visibility into network performance, security threats, and application behaviour. Its seamless integration into existing network architectures ensures uninterrupted operations, even during critical moments, providing businesses with the necessary insights to swiftly identify irregularities or potential security breaches.
In addition, DDoS resilience testing holds significant importance in fortifying a business's cybersecurity defences. By subjecting networks to regular resilience testing, businesses can evaluate their systems' ability to withstand distributed denial-of-service attacks. Such testing allows businesses to identify potential vulnerabilities and weaknesses, empowering them to implement the necessary defences and optimise network configurations. Through these comprehensive measures, businesses can bolster their networks, ensuring they can withstand DDoS attacks and continue to deliver uninterrupted services to their users.
Boost Your Network Security With These Essential Tips for Businesses
When it comes to safeguarding their networks, businesses must adopt a robust security framework. By following a set of best practices, they can gain valuable insights into network performance, ensure an optimal user experience, detect and address issues proactively, and maintain overall network health and security.
- Get to Know Your Network: Start by establishing baselines for network performance to understand what's normal. This way, you can easily spot any deviations or anomalies that might indicate potential issues.
- Keep a Close Eye on Performance: Implement a comprehensive network performance monitoring system that provides real-time visibility into network performance, end-user experience, and application behaviour. Monitor network flow data, packet data, and infrastructure metrics to stay on top of things.
- See It from the User's Perspective: Gain valuable insights into the actual user experience by monitoring network performance from the end-user perspective. Make use of accurate and timely understanding of end-user experience scores.
- Dig Deep into the Data: Analyse network data using advanced techniques like machine learning algorithms. Look for solutions that offer deep insights into network KPIs (Key Performance Indicators) and can help you identify and prioritise the root causes of performance issues.
- Capture the Evidence: Make sure to capture and retain all relevant data, including packet-level data, flow records, and system logs. This way, you can conduct thorough post-event analysis and troubleshooting, leading to quick identification and resolution of network performance issues.
- Stay One Step Ahead: Set up alerts based on performance thresholds to proactively detect and address potential network issues before they become critical. This helps minimise downtime and keeps your network running smoothly.
- Team Up for Success: Foster collaboration between network operations (NetOps) and security operations (SecOps) teams. Network performance monitoring solutions can enhance security by providing detailed visibility into network traffic and supporting cybersecurity investigations.
- Automate and Streamline: Take advantage of automation and streamlined workflows to speed up problem identification and root cause analysis. This leads to faster issue resolution, less manual work, and improved operational efficiency.
- Conduct DDoS Resilience Testing: Regular DDoS resilience testing should be conducted alongside other security practices to assess the network's resilience against distributed denial-of-service attacks. This testing allows businesses to identify potential vulnerabilities and reinforce their defences, ensuring the network's ability to withstand and mitigate the impact of such attacks.
- Stay Scalable and Adaptable: Choose network performance monitoring solutions that can scale with your growing network complexity, including distributed environments, remote user access, and cloud-hosted assets. Ensure the solutions can adapt to new technologies and provide visibility across different hosting environments.
- Always Improve: Continuously monitor trends and perform ongoing analysis to detect performance degradations or security threats. Regularly review and refine your network monitoring strategies to optimise performance, maintain security, and align with your evolving business objectives.
The Bottom Line
Businesses must prioritise network monitoring and DDoS resilience testing as crucial components of their cybersecurity strategies. By adopting proactive measures, leveraging robust tools, and following best practices, organisations can mitigate risks, protect valuable data, and maintain the security and integrity of their networks in the face of the ever-growing cyber threat landscape.