Discover the Secret to Robust Cyber Resilience with Advanced Cyber Ranges - Are You Ready?
The security requirements for testing new software releases, IT infrastructure, or setting up a Cyber Range are much more stringent than in regular commercial markets. As a result, a "Permissions based Architecture" is required to ensure that only authorized individuals have access to certain data or functions. Additionally, each communication path must be "Hardened," which means that they need to be made more secure to protect against crosstalk, which is when information leaks between communication channels. This can happen when unauthorized users access data that they should not have access to or when information is accidentally transmitted to the wrong channel.
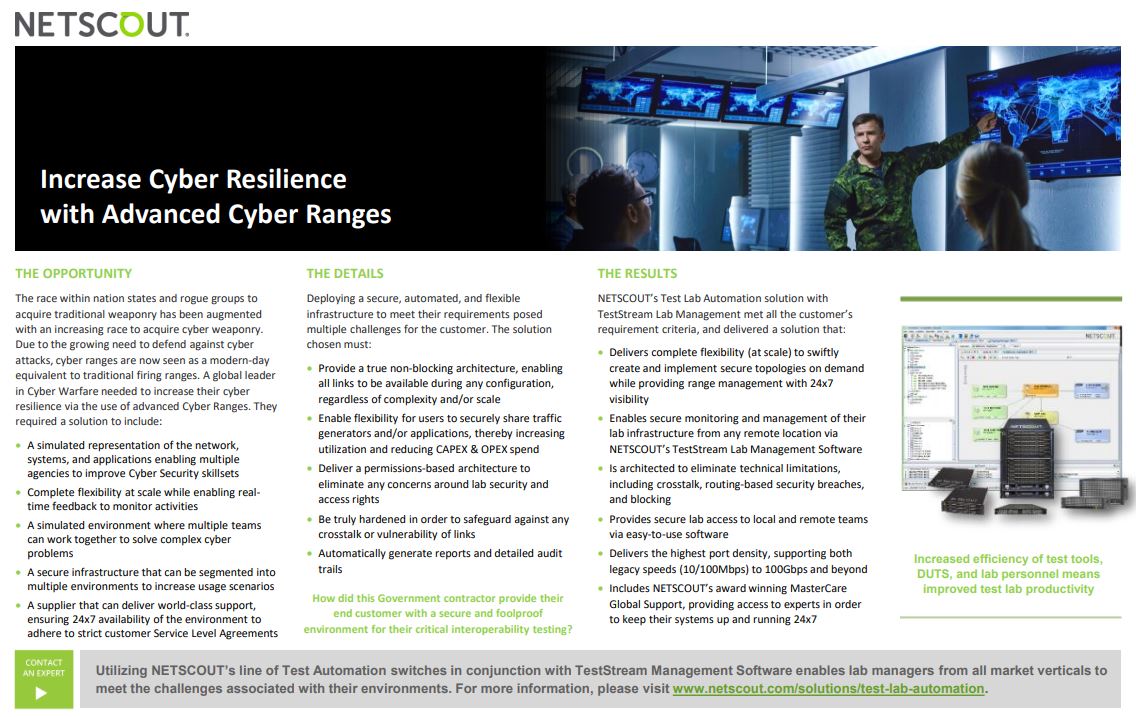
Setting up a secure, automated, and transparent lab infrastructure presents significant challenges for government agencies and their suppliers. The process of developing a precise simulated representation of their network, system, or application environments while maintaining security is not an easy task. On top of that, concerns about CapEX (capital expenditure) and OpEX (operational expenditure) spending and maximizing tool utilization only add to the complexity and difficulty of the task.
In order to make the most of test tools, it's important for them to be scalable and flexible. However, flexibility can also be risky if it means making changes to the network topology at short notice, as this can lead to security vulnerabilities. NESTSCOUT has come up with a solution that addresses and removes these concerns.
This Solution set, developed through years of experience within this market vertical, are recognized as the most secure, fully redundant and transparent in the industry today and we would like the opportunity of speaking with you and how they are utilized. Please call us on 1800 COVERTEL (1800 268 378) or contact us here to schedule a chat.
What is Cyber Range?
A Cyber Range is a secure virtual environment used for testing and training in the field of cybersecurity. It provides a simulated network and system environment where cybersecurity professionals can practice and refine their skills in a safe and controlled setting without the risk of compromising real-world systems or data. Cyber Ranges can be used to simulate a wide range of scenarios, such as cyber attacks, malware infections, or system failures, and to test the effectiveness of security tools and protocols in preventing and responding to these incidents. They can also be used to develop and test new security technologies and techniques. Cyber Ranges are commonly used in government and military organisations, as well as in the private sector for cybersecurity training and testing.
